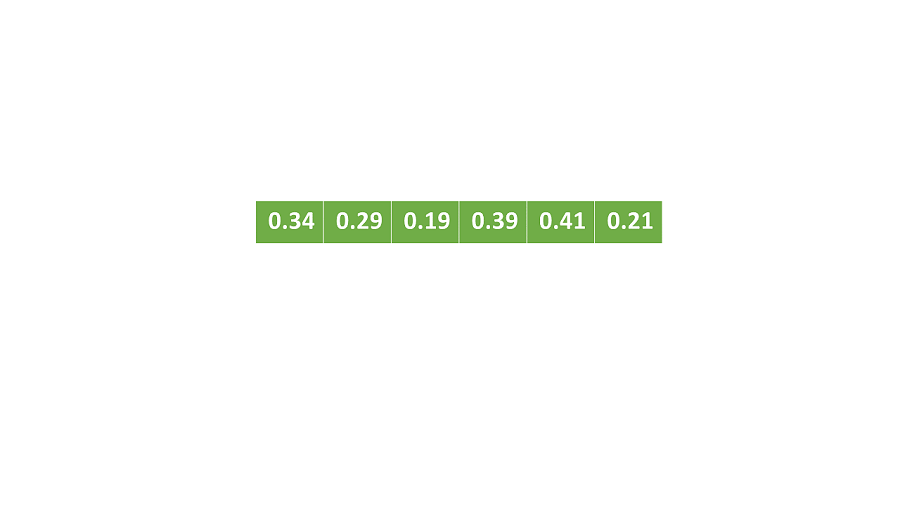
Bucket Sort: A Complete Guide
A bucket sort is a sorting algorithm that divides an array's components into several buckets. Each of those buckets is sorted separately using a different sorting method or applying Bucket sort on it cyclically. It's a distribution sort, which is a broadening of…
How to Restore Deleted Game Data on Windows
‘I wanted to free up some space to get Shadow of Mordor on my PC, so deleted a few old games. But mistakenly removed some wrong files. They were of my ongoing game progress. How can I recover deleted game…
5 Cybersecurity Solutions Every Business Needs
As the number of threats to businesses and individuals increases, it is vital to have cybersecurity solutions in place. Here are five services that every business needs. 1. Endpoint Security Endpoint security provides a way to monitor and control all…
Five features needed for IOT Data Processing
The IoT is primarily concerned with the data collected from connected sensors. IoT devices are objects with IP addresses that can collect and transfer data over the Internet, and generate a large amount of data at a high rate. Moreover,…
Data Access Problems and Flexible Integration Solutions
Seamless integration platforms allow you to access new frontiers in the world of enterprise optimization. You might be wondering if an ERP system is the next step for your enterprise. There’s no doubt that ERPs can be incredibly helpful for…
Low-cost 6-20 GHz Microwave Spectrum Analyzer
SAF Tehnika has added a low-cost spectrum analyzer device to their Spectrum Compact range of ultra-portable handheld RF spectrum analyzers that support 6 GHz–20 GHz. The new Spectrum Compact microwave analyzer offers best-in-class price/performance and great durability at an affordable…
15 Proven Ways to Improve Your Team Morale
Team morale is a crucial ingredient for a successful company. It predicts success and failure better than any other factor, including recruiting quality employees. High morale is the sign of a healthy team, and low morale indicates something is going…
How Will Machine Learning Impact Mobile Apps
Machine learning algorithms are helping developers in developing apps to offer more personalized services. But what other impacts are there? Let’s have a look. Influence of Machine Learning Algorithms on Mobile Apps If you are a regular user of platforms…
What Not to Keep in Your Mailbox
Cybersecurity is a fickle matter. Today, you might be completely safe and browsing the web confidently. However, the time might come when your data, identity, or finances will be put in danger. And, of course, you can never predict when…
What Benefits Any Business Can Get With Chatbots?
Many business owners might think that their business will not have much to benefit from chatbots. This is a very common reaction when new technology is introduced, it's completely understandable. The problem occurs when these businesses choose decisively not to…